Blog
-
Install Node with NVM
Introduction: Alternative Installation Methods for Node.js When it comes to installing Node.js on Ubuntu 22, there are several methods available. However, one method that is highly recommended is using the Node Version Manager (nvm). This tool allows you to manage multiple versions of Node.js and provides a seamless way to switch between them. In this…
-
Lynis – Security, virus, adware scan for Linux
In the world of cybersecurity, maintaining the security and integrity of your system is of paramount importance. Regularly auditing your system can help identify potential vulnerabilities and ensure that your system is protected against various security threats. One tool that stands out in the field of system auditing is Lynis. What is Lynis? Lynis is…
-
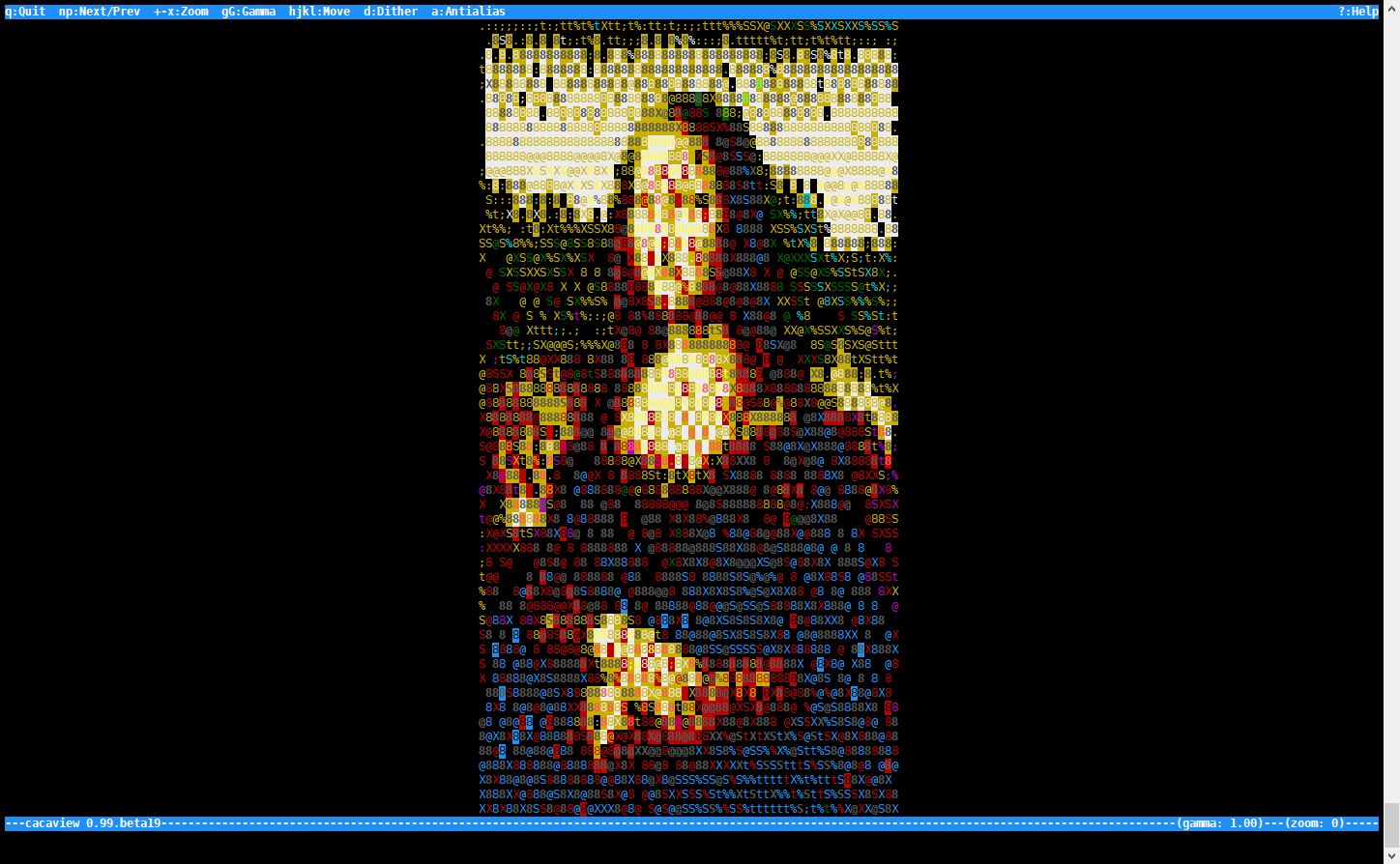
Viewing images on a remote console
Using a remote console to log on a linux environment, there usually is no graphical interface (hence why it is called remote command-line) There are a few tools that can give you an idea what the image looks like, tools like caca-utils will render an image and return an array of ascii characters to your…
Got any book recommendations?