Blog
-
Chrome and Firefox Phishing Attack Uses Domains Identical to Known Safe Sites
Update on April 19th at noon Pacific time: Chrome has just released version 58.0.3029.81. We have confirmed that this resolves the issue and that our ‘epic.com’ test domain no longer shows as ‘epic.com’ and displays the raw punycode instead, which is ‘www.xn--e1awd7f.com’, making it clear that the domain is not ‘epic.com’. We encourage all Chrome users to…
-
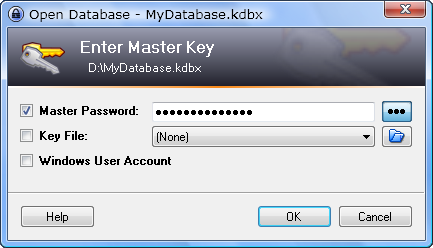
Review: Keepass
Keepass is a Password Manager, which helps you to remember your password and make secure passwords for you. Securing your online accounts is becoming more and more important, and using unique passwords for each account is very important to avoid that your other accounts get hacked when a single website or service leaked your information. This way…
-
Upcoming program reviews
I will soon start publishing some reviews of programs that I use daily. These range from password managers, file managers, security tools, development tools, image editing and more. Each post will have an in-depth explanation of how you can use the program and configure it to your needs. The first program I will introduce to…
Got any book recommendations?
You must be logged in to post a comment.